Healthcare Cybersecurity: Is Patient Data Actually Secure?
| 6 Min Read

Cybersecurity continues to instill panic in businesses and increase spending in IT.
Between 2013 and 2018, the number of cybersecurity breaches grew more than 33 percent a year on average, according to Milton Ezrati, chief economist for New York-based communications firm Vested. Cybersecurity spending jumped from $40 billion in 2013 to $66 billion in 2018.
It’s hard to deny the overall growth of cybersecurity. In 2004, the global cybersecurity market was worth $3.5 billion. That figure increased to $152.7 billion in 2018 and is expected to reach $248.3 billion by 2023, according to research firm MarketsandMarkets.
One industry is on high alert: healthcare cybersecurity. Healthcare data breaches have increased dramatically in recent years, and they may not let up anytime soon. MarketsandMarkets singled out healthcare cybersecurity as the highest-growing industry for 2018 to 2023, due to how medical data and digital medical devices used are prone to advanced threats. Finally, healthcare is ill-prepared to meet current and future threats. As a literature review published in Technology in Healthcare found, “the healthcare industry is a prime target for medical information theft as it lags behind other leading industries in security vital data.”
The Rise of Healthcare Data Breaches
The number of annual healthcare data breaches increased 70 percent from 2010 to 2017, according to a study published in JAMA Network (Journal of the American Medical Association). With the exception of 2015, the number of breaches increased each year.
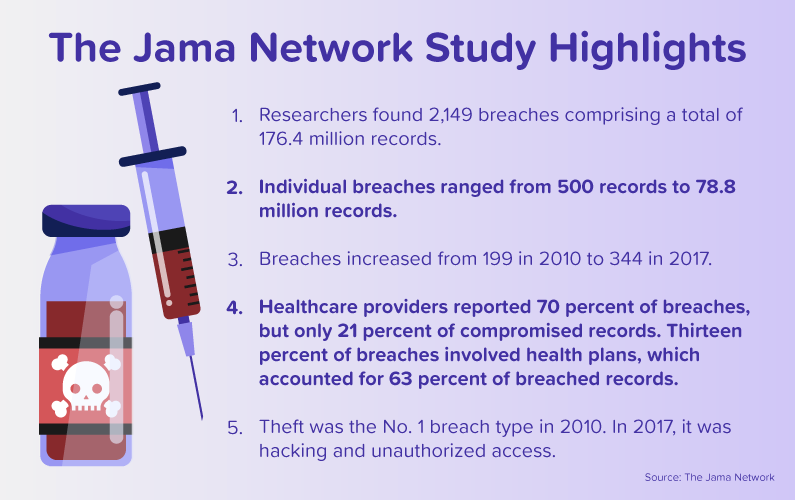
The study examined healthcare data breaches that were reported to the Department of Health and Human Services (HHS). Since 2009, breaches of health information protected under HIPAA must be reported to the HSS. If breaches include 500 or more records, they are tracked in a public database.
Researchers linked the rise of healthcare data breaches to the use of electronic medical records. The Health Information Technology for Economic and Clinical Health Act (HITECH Act) in 2009 introduced strong incentives for doctors and hospitals to use electronic medical records. Forbes reported that in 2006, 46 percent of hospital emergency departments used an electronic health record system, and that figure increased to 84 percent in 2011.
The JAMA study suggested that healthcare data breaches may continue to increase, and that is certainly true, based on data from the first and second quarter of 2018. Healthcare security firm Protenus reported on the number of breaches disclosed to the HSS and the media.
- The first quarter of 2018 saw 110 incidents. Details were disclosed for 84 of those events, affecting 1,129,744 patient records. The largest breach involved an Oklahoma-based organization that affected 279,856 patient records.
- The second quarter of 2018 saw 142 incidents. Details were disclosed for 116 of these events, affecting 3,143,642 patient records. The largest breach involved a Sacramento-based office of the Department of Developmental Services, which affected 582,174 patient records.
How Is Data Compromised?
Major Trends
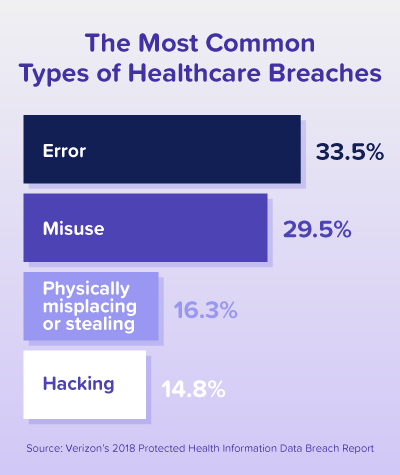
Healthcare data breaches can take many forms, but the most significant threat is unique. More than 50 percent of incidents involved insiders, according to a report from Verizon, which makes healthcare the only industry in which internal actors are the biggest threat to an organization.
Verizon’s 2018 Protected Health Information Data Breach Report examined 1,368 incidents across 27 countries. Of the 58 percent of incidents involving insiders, most were driven by financial gain, like tax fraud or opening up lines of credit with stolen information (48 percent). Others were marked by fun or curiosity in looking up the personal information of celebrities or family members (31 percent), or simple convenience (10 percent).
The significance of insiders and healthcare data is hard to overstate. Protenus reported that on average, if an employee breaches patient privacy once, there is a greater than 30 percent chance that the person will do so again in three months’ time. The figure rises to more than 66 percent in a years’ time.
Another major trend in Verizon’s report was the presence of ransomware. Of incidents involving malicious code, 70 percent were classified as ransomware. Ransomware is a type of malware prevents users from accessing their system or personal files. The program demands a ransom payment to regain access. It’s rather easy for employees to download ransomware clients without knowing it. Most commonly, ransomware is obtained through unsolicited email messages. Users can download booby-trapped attachments or clicking on links to malicious websites, which can result in ransomware clients infiltrating a network or device.
Newer Methods of Attack
Healthcare organizations must be on guard against several threats to sensitive data. Unfortunately, that includes newer and emerging tactics from cybercriminals.
In early 2018, Symantec released information on a new attack group called Orangeworm. That group is targeting large international corporations operating within the healthcare sector in the United States, Europe, and Asia. After careful and deliberate planning, Orangeworm launches an attack.
The attack is focused on computers that control medical imaging devices like MRIs and X-rays, as well as devices patients use to fill out consent forms. After infiltrating a victim’s network, Orangeworm deploys a backdoor Trojan program to gain remote access to the compromised computer. The malicious software then gathers information from the victim’s network, including configuration information, account policy information, accounts with admin access, network shares and user groups, and more.
If the virus finds something in the system of value, the backdoor Trojan will copy itself, spread across the network and infect other computers. This aggressive plan demonstrates that the malware isn’t particularly concerned about being discovered, which is part of the reason that it’s so successful.
Examining the Future of Healthcare Cybersecurity
The trends in healthcare cybersecurity are easy to spot. Healthcare data breaches have increased sharply. Insiders pose an extremely dangerous and hidden risk to organization. Additionally, given the digital nature of medical data and medical devices, outsiders have plenty of potential targets.
Those trends are only the basics for the state of healthcare cybersecurity, but they showcase how it’s the fastest-growing industry in data security. More professionals are sorely needed. In its second quarter report on healthcare security, Protenus found that in hospital teams responsible for responding to insider threats, one investigator monitors an average of nearly 4,000 employees. It should come as no surprise that Technology in Healthcare singled out healthcare as falling behind other industries in securing data.
The increased need for professionals in healthcare cybersecurity is reflected in the job outlook for information security analysts, who are tasked with protecting an organization’s computer networks and systems. Employment of those professionals is expected to increase a staggering 28 percent by 2026, according to the Bureau of Labor Statistics. That’s nearly four times the average for all occupations, and it’s the strongest of all major computer and information technology occupations, The median annual wage for information security analysts is $95,510.
An online bachelor’s in Computer Science can help you pursue a career in cybersecurity. You’ll gain the knowledge and skills needed to work as an information security analyst, or in roles like systems analyst, operations manager, and IT strategist.
In all of these programs, you can enjoy small class sizes with a personal learning environment geared toward your success. Learn from knowledgeable faculty who have industry experience. Get started with CSP today.
Also published on Medium.